HybridPetya ransomware bypasses UEFI Secure Boot to lock Windows PCs at the boot level
A new strain of ransomware called HybridPetya is raising alarms for its ability to attack a PC before Windows even loads. Discovered by researchers at ESET, the malware can bypass UEFI Secure Boot and tamper with a system’s EFI System Partition, effectively bricking the machine from the ground up and holding the entire drive hostage.
Secure Boot is designed to verify that only trusted, signed code runs during startup. HybridPetya undercuts this protection on systems using UEFI with GPT partitioning, then adds, deletes, or modifies boot files on the EFI partition to lock and encrypt the rest of the drive’s data. In practice, that prevents the device from booting into Windows and cuts off easy access to files.
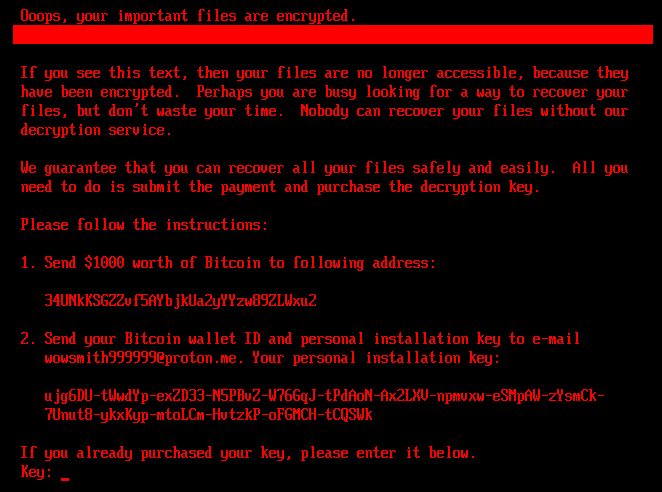
Victims are shown a ransom note claiming that all files have been encrypted. The demand instructs users to send US$1,000 worth of Bitcoin to a specified wallet, then email their Bitcoin wallet address and a generated installation key to a ProtonMail address to receive a decryption key.
There’s a silver lining. As of September 12, researchers had not observed any real-world attacks, suggesting HybridPetya is still in testing or proof-of-concept stages. Even better, the vulnerability leveraged by this malware was addressed in a Windows security update released in January 2025. Systems fully updated with the latest Windows patches should be protected against this specific exploit.
Key takeaways:
– What it is: HybridPetya is boot-level ransomware capable of bypassing UEFI Secure Boot and corrupting the EFI boot partition to block Windows from starting and encrypt data.
– How it spreads: The discovery is in a research phase, with no widespread campaigns reported yet.
– Ransom demand: US$1,000 in Bitcoin, plus instructions to contact the attackers via email with a unique installation key.
– Protection status: Microsoft patched the underlying vulnerability in the January 2025 Patch Tuesday update; fully updated Windows devices are expected to be safe.
– Other platforms: It’s unclear whether macOS or Linux are affected.
How to reduce your risk now:
– Install all available Windows updates, including the January 2025 security rollup and any subsequent patches.
– Keep UEFI/BIOS firmware up to date and ensure Secure Boot remains enabled.
– Maintain recent, offline backups so you can recover without paying a ransom.
– Be cautious with unsolicited emails, downloads, and removable media, which are common infection vectors for ransomware.
Bottom line: HybridPetya is a serious reminder that ransomware is evolving to target systems at the boot level. While active, widespread attacks haven’t been seen, outdated machines are at the highest risk. Staying current with Windows updates and practicing strong backup and security hygiene are the best defenses.