The cybersecurity community recently witnessed a concerning development regarding the integrity of the Windows Update Process. During the Black Hat USA 2024 conference, revelations emerged about a significant threat where attackers could potentially hijack this process to force a ‘downgrade’ of the system. To the user’s detriment, this would effectively roll back critical security updates and patches, leaving their system vulnerable to a range of attacks that exploit old vulnerabilities.
This strategy involves crafting a tailored ‘downgrade’ by manipulating the system’s action list XML file using a custom tool. This tool skillfully navigates around the standard verification steps and even the Trusted Installer that Windows relies on for security during updates. Moreover, it can convince the system that it is fully updated, leaving users unaware of the vulnerability.
This vulnerability is particularly concerning because it targets a foundational aspect of system security — the Windows Update process itself — which has already been compromised in the past. An example of this is the 2023 discovery of the BlackLotus UEFI Bootkit which also utilized a downgrade approach to undermine Windows Update, specifically targeting the VBS UEFI locks.
The manipulation of the Windows Update process unlocks the door for malicious actors to employ ‘zero-day’ attacks, which otherwise would be neutralized by a fully up-to-date system. These attacks enable privilege escalation, resulting in unauthorized administrative power within the system.
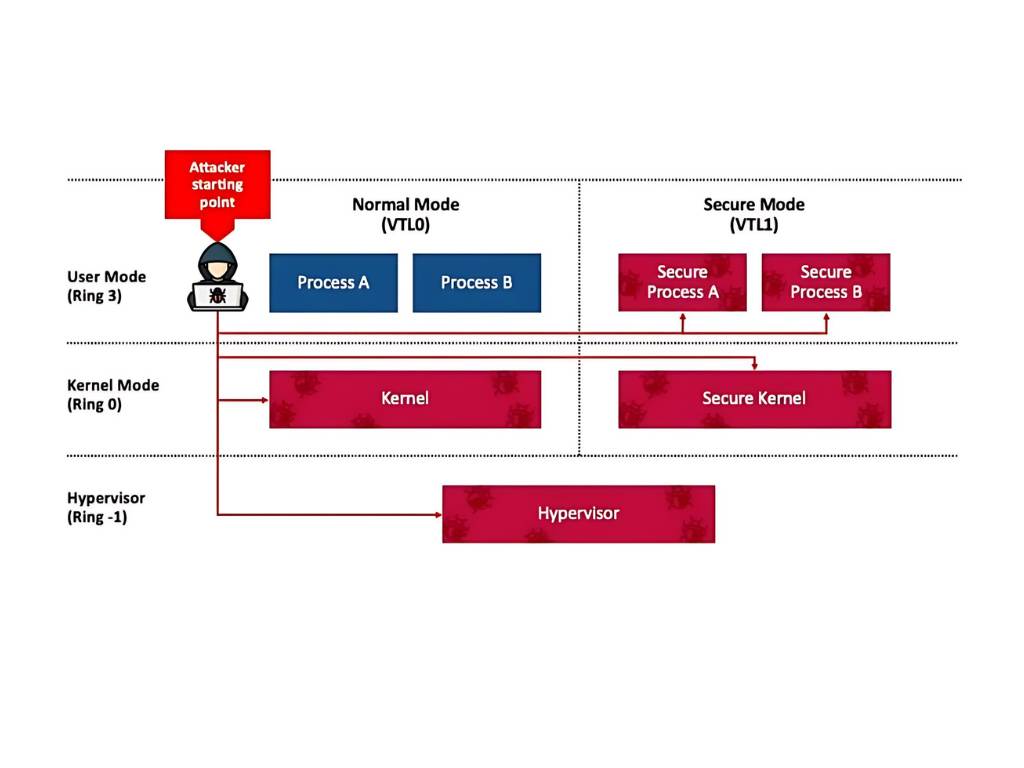
Alon Leviev, the SafeBreach researcher who revealed the vulnerability, pointed out that this exploitation could compromise Windows virtualization-based security (VBS), along with related features such as Credential Guard and Hypervisor-Protected Code Integrity (HVCI), even when they are enforced with UEFI locks.
Leviev has reported these concerns to Microsoft and is already in dialogue with them to address these issues. As of now, Microsoft is striving to develop a security update that will safeguard against the invalidation of VBS systems and will also be providing customers with guides containing mitigations or risk reduction guidance.
What makes these attacks particularly daunting is their inherent undetectability—making them transparent and unobservable to users. Therefore, relying solely on visible cues from the system is inadequate for ensuring its security.
Users and IT professionals must stay vigilant and seek out knowledge on the functioning of their system updates to protect their systems effectively. Even as experts work on resolving these vulnerabilities, staying informed and understanding the mechanisms behind updates should be considered crucial in safeguarding against such downgrade attacks.
For those keen on delving deeper into the specifics of the exploit and the technical intricacies involved, further information is available through several cybersecurity resources and expertise-sharing platforms. These resources can offer a closer look at the nature of the exploit and the ways to potentially identify or mitigate its risk.