## Exploring the Security Flaw in Apple’s M-Series Chips
### The Vulnerability: Unveiling “GoFetch”
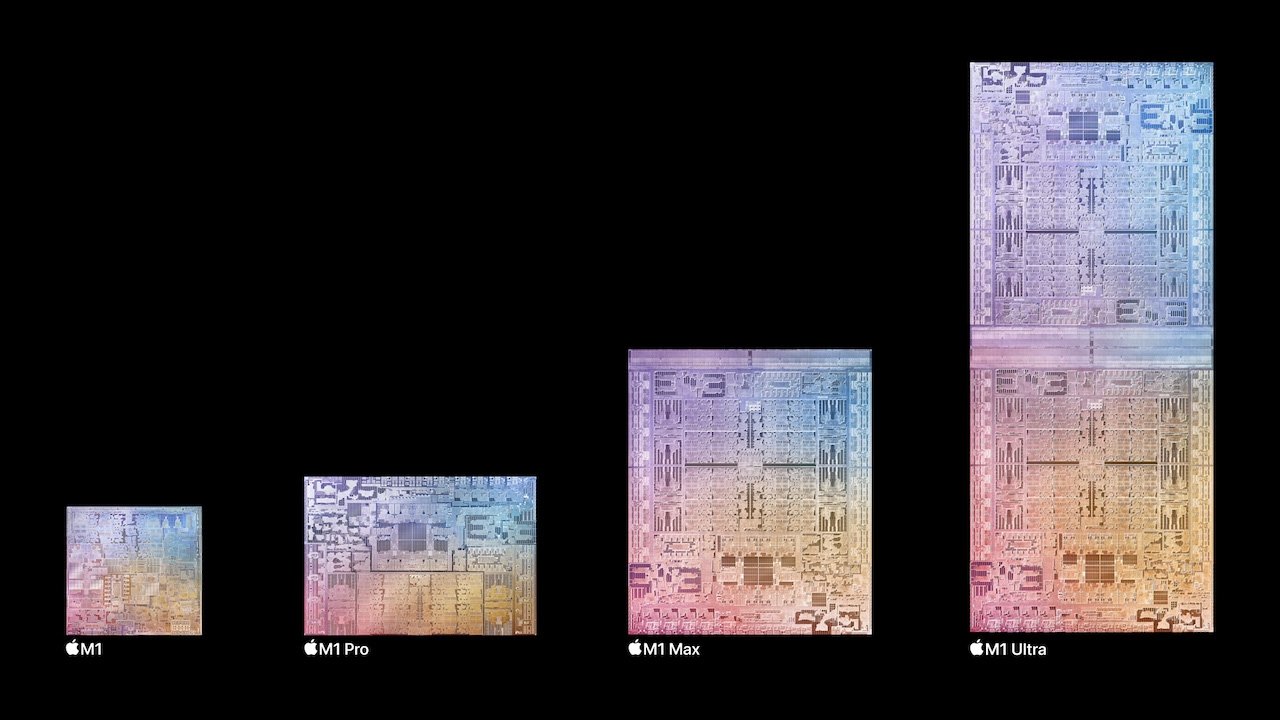
Recent findings in the tech security landscape have unveiled a significant security flaw within Apple’s M1 and M2 chip families. This vulnerability, referred to as “GoFetch,” poses a potential risk to the encryption key safety used in various cryptographic services.
The fault lines within Apple’s silicon are bound to its microarchitecture, which facilitates a “side-channel” that can be manipulated to extract sensitive data, such as cryptographic keys essential for tasks like user authentication and data encryption. Researchers have demonstrated the severity of this vulnerability by developing an application named after the flaw itself. This application can recover critical encryption keys within a time range from less than an hour up to around 10 hours.
### Implications of the Security Breach
The gravity of “GoFetch” is evident from the range of encryption standards it can compromise, including advanced encryption methods like 2048-bit RSA keys, DH-2048, Kyber-512, and Dilithium-2. The risk is particularly acute for devices wielding Apple’s M1 and M2 chips because the flaw is embedded deep within the chip design, rendering superficial fixes ineffective.
For developers using Apple’s CryptoKit to streamline security in apps, this revelation is particularly troubling as it isn’t a software-level issue. Rather, it implicates the fundamental design of the chips themselves.
### Addressing the Flaw: Performance Compromises
Addressing this vulnerability is complex, as it is intertwined with the hardware’s design. The likely recourse will be a software patch issued by Apple, a solution reminiscent of what was implemented for previous processor vulnerabilities like Meltdown and Spectre, which impacted several processor brands.
This fix, while necessary, could bear the cost of reduced processing performance – an outcome that could concern users over slowed functionalities. Past incidents have shown that patches for hardware-level security issues can degrade performance noticeably, citing a performance drop in Intel processors post-Spectre-V2 patch implementation as a prelude to what might be expected for affected Apple devices.
### Looking Ahead
Apple hasn’t yet made an official statement regarding the reported vulnerability, but it’s anticipated that they are on the path to developing a remedy. The research indicating the flaw was brought to Apple’s attention, and the tech community is awaiting a response, which could involve a formal acknowledgment or the release of a patch.
The “GoFetch” incident is a reminder of the ever-evolving challenges in tech security and the importance of constant vigilance and innovation to stay ahead in the cybersecurity game. It also highlights the delicate balance between security and performance – a trade-off that consumers and manufacturers alike must navigate thoughtfully.
### Practical Insights for Users
For users concerned about the security of their Apple silicon-based devices, it is important to keep all software up to date, including the operating system, as updates typically include security patches. Also, consider utilizing additional security measures, such as using encrypted messaging apps, secure password managers, and two-factor authentication where available to add layers of protection to your digital activities.
Stay informed of official announcements from Apple and be ready to update your devices when a fix becomes available. In the interim, practice caution with sensitive transactions and stay alert to unusual device behavior that may indicate a security compromise.